Data Security and Encryption with PreciseFP
Ensure Your Financial Planning Firm Gets the Highest Level of Protection with the Best Data Encryption Security There Is
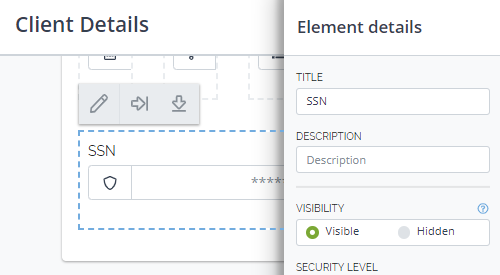
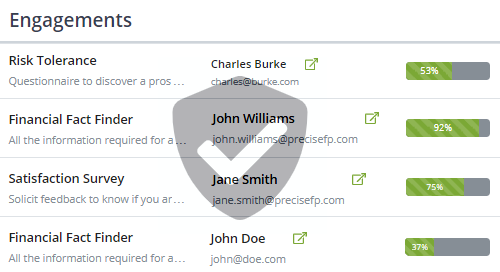
PreciseFP’s data security starts with a secure connection to and from our servers, via 256-bit SSL encryption. Data is further encrypted at rest and is stored in secure databases. Data that you collect with PreciseFP can only be accessed by you and those to whom you grant control. Our development staff can never access sensitive client data, and our support staff can only access it with your explicit permission as needed for addressing issues.
Physical Security
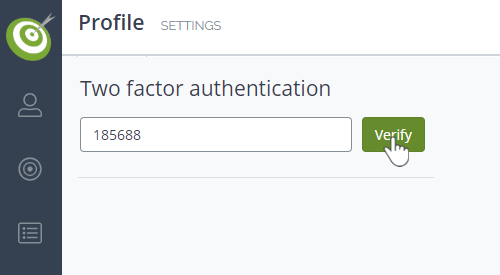
PreciseFP servers are housed in nondescript facilities in the United States of America. These critical facilities have extensive setback and military grade perimeter control berms, plus natural boundary protection. Physical access is strictly controlled at the perimeter and building ingress points, monitored by professional security staff using video surveillance and state-of-the-art intrusion detection systems. Authorized staff must pass two-factor authentication no fewer than three times to access data center floors. All visitors and contractors are required to present identification, are signed in, and escorted by authorized staff.
GDPR Compliance
The General Data Protection Regulation (GDPR) requires businesses to protect the personal data and privacy of EU citizens. Companies that collect or process personal data of EU citizens must comply with the regulation or risk fines as high as 20 million euros or 4% of their annual revenue. We address the six principles of GDPR and we are here to help everyone using PreciseFP achieve GDPR compliance too. Read more about how we address GDPR here.
Our Security Commitment
We are committed to constantly improving the security of our application. We work closely with expert security consultants who perform penetration tests and audits on our systems regularly. Our development team ensures that industry best practices are followed with all new features we deploy, and that all code is reviewed and tested before deployment to production. We also employ always-on software scanners to ensure our code, servers, and database infrastructure are secure. In the event of a breach, our team will be notified immediately so necessary steps can be taken to restore security right away. To request a copy of our security policies and procedures, please contact us.